Manage Cyber Risk
From Strategy to Security to Success
Secure Your Business with the Cyber Advisory and Solutions Leader

What's New at Optiv

E-book
Modernizing Your Security Operations
Consider these key questions when building a SecOps strategy.

Report
2024 Cybersecurity Threat and Risk Management Report
Gain budgeting insights from Ponemon Institute and Optiv.

Interactive Experience
CISO Periodic Table
Review the threats and opportunities facing today's CISO.
Solutions
Optimize Your Security Program to Help Drive Unique Business Outcomes
- Ensure Compliance
- Protect Your Business
- Maximize Effectiveness
- Build Resilience

Solutions
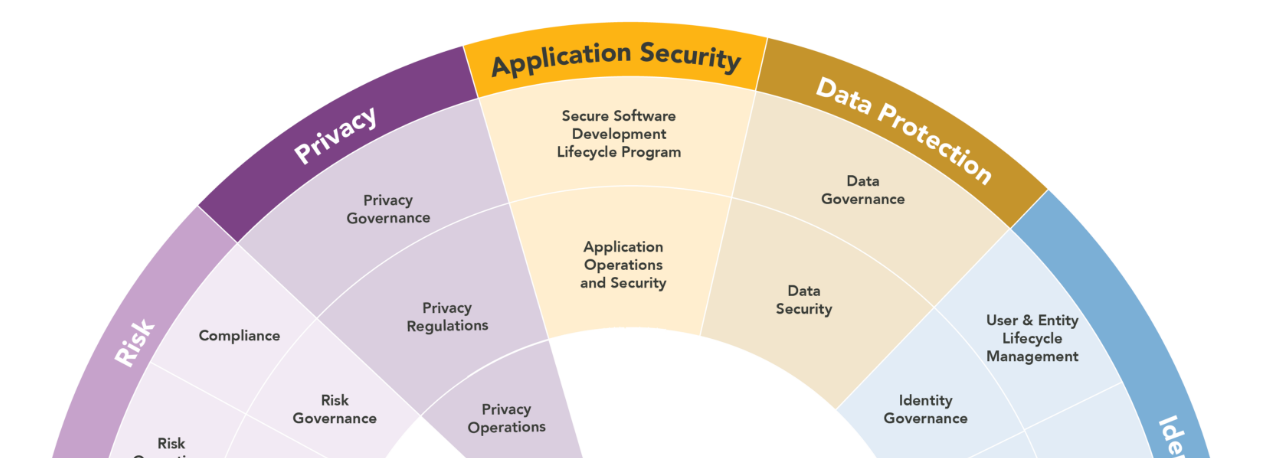
Simplify Cybersecurity with Optiv Market SystemTM
A reference architecture for cybersecurity. The only taxonomy of its kind, OMSTM is how our ~6,000 clients experience cybersecurity.
Start with Optiv Market System
Services
How Well Do You Know Your Security Tools?
The average enterprise uses between 70 to 90 security tools. Consolidate your tools to reduce redundancies and complexity.
Start with Cybersecurity Consolidation

Infographic
Optiv's Cybersecurity Technology Map
Explore a simplified view of cybersecurity technologies across 450+ vendors and 40+ categories.

A Category of One
We Manage Cyber Risk So You Can Secure Your Full Potential
Our single focus is supporting your secutity journey end-to-end, from strategic planning and vendor selection to solution design, implremenation and management. Our goal is to ensure you get the most value - from pricing through execution.
~0
Clients across every major vertical
0+
Client service hours delivered
0+
Security certifications
0+
Former CISOs
Technology Sourcing Made Easy
Spend less time sourcing technology and more time using it by leveraging our relationships with 450+ technology vendor partners. Your designated Optiv operations team can manage reporting, quoting and renewals on your behalf for a faster, more accurate buying process.
Trusted By ~6,000 Clients
Proactive solutions with repeatable results. It's why we serve 73% of the Fortune 100 and generate 95% repeat clients.
"We believe that Optiv is on the short list of valued partners."
CISO, Healthcare Company
"We chose Optiv because you guys ARE SECURITY."
Director, Technology Company
"We share a lot of the same values as Optiv and appreciate partnering with an organization with our alignment."
CIO, Law Firm
Let's Secure
Greatness Together

















